Search Results for author: Alex Kot
Found 22 papers, 9 papers with code
Splitting vs. Merging: Mining Object Regions with Discrepancy and Intersection Loss for Weakly Supervised Semantic Segmentation
no code implementations • ECCV 2020 • Tianyi Zhang, Guosheng Lin, Weide Liu, Jianfei Cai, Alex Kot
Finally, by training the segmentation model with the masks generated by our Splitting vs Merging strategy, we achieve the state-of-the-art weakly-supervised segmentation results on the Pascal VOC 2012 benchmark.
Improving Concept Alignment in Vision-Language Concept Bottleneck Models
1 code implementation • 3 May 2024 • Nithish Muthuchamy Selvaraj, Xiaobao Guo, Bingquan Shen, Adams Wai-Kin Kong, Alex Kot
Concept Bottleneck Models (CBM) map the input image to a high-level human-understandable concept space and then make class predictions based on these concepts.
Safeguarding Medical Image Segmentation Datasets against Unauthorized Training via Contour- and Texture-Aware Perturbations
no code implementations • 21 Mar 2024 • Xun Lin, Yi Yu, Song Xia, Jue Jiang, Haoran Wang, Zitong Yu, Yizhong Liu, Ying Fu, Shuai Wang, Wenzhong Tang, Alex Kot
This is particularly true for medical image segmentation (MIS) datasets, where the processes of collection and fine-grained annotation are time-intensive and laborious.
Suppress and Rebalance: Towards Generalized Multi-Modal Face Anti-Spoofing
3 code implementations • 29 Feb 2024 • Xun Lin, Shuai Wang, Rizhao Cai, Yizhong Liu, Ying Fu, Zitong Yu, Wenzhong Tang, Alex Kot
Face Anti-Spoofing (FAS) is crucial for securing face recognition systems against presentation attacks.
MIMIC: Mask Image Pre-training with Mix Contrastive Fine-tuning for Facial Expression Recognition
no code implementations • 14 Jan 2024 • Fan Zhang, Xiaobao Guo, Xiaojiang Peng, Alex Kot
In addition, when compared with the domain disparity existing between face datasets and FER datasets, the divergence between general datasets and FER datasets is more pronounced.
BenchLMM: Benchmarking Cross-style Visual Capability of Large Multimodal Models
2 code implementations • 5 Dec 2023 • Rizhao Cai, Zirui Song, Dayan Guan, Zhenhao Chen, Xing Luo, Chenyu Yi, Alex Kot
Large Multimodal Models (LMMs) such as GPT-4V and LLaVA have shown remarkable capabilities in visual reasoning with common image styles.
 Ranked #1000000000 on
Visual Question Answering
on MS COCO
Ranked #1000000000 on
Visual Question Answering
on MS COCO
S-Adapter: Generalizing Vision Transformer for Face Anti-Spoofing with Statistical Tokens
2 code implementations • 7 Sep 2023 • Rizhao Cai, Zitong Yu, Chenqi Kong, Haoliang Li, Changsheng chen, Yongjian Hu, Alex Kot
Face Anti-Spoofing (FAS) aims to detect malicious attempts to invade a face recognition system by presenting spoofed faces.
Hyperbolic Face Anti-Spoofing
no code implementations • 17 Aug 2023 • Shuangpeng Han, Rizhao Cai, Yawen Cui, Zitong Yu, Yongjian Hu, Alex Kot
To further improve generalization, we conduct hyperbolic contrastive learning for the bonafide only while relaxing the constraints on diverse spoofing attacks.
Rehearsal-Free Domain Continual Face Anti-Spoofing: Generalize More and Forget Less
no code implementations • ICCV 2023 • Rizhao Cai, Yawen Cui, Zhi Li, Zitong Yu, Haoliang Li, Yongjian Hu, Alex Kot
To alleviate the forgetting of previous domains without using previous data, we propose the Proxy Prototype Contrastive Regularization (PPCR) to constrain the continual learning with previous domain knowledge from the proxy prototypes.
Audio-Visual Deception Detection: DOLOS Dataset and Parameter-Efficient Crossmodal Learning
1 code implementation • ICCV 2023 • Xiaobao Guo, Nithish Muthuchamy Selvaraj, Zitong Yu, Adams Wai-Kin Kong, Bingquan Shen, Alex Kot
Despite this, deception detection research is hindered by the lack of high-quality deception datasets, as well as the difficulties of learning multimodal features effectively.
Raw Image Reconstruction with Learned Compact Metadata
1 code implementation • CVPR 2023 • YuFei Wang, Yi Yu, Wenhan Yang, Lanqing Guo, Lap-Pui Chau, Alex Kot, Bihan Wen
While raw images exhibit advantages over sRGB images (e. g., linearity and fine-grained quantization level), they are not widely used by common users due to the large storage requirements.
Rethinking Vision Transformer and Masked Autoencoder in Multimodal Face Anti-Spoofing
no code implementations • 11 Feb 2023 • Zitong Yu, Rizhao Cai, Yawen Cui, Xin Liu, Yongjian Hu, Alex Kot
In this paper, we investigate three key factors (i. e., inputs, pre-training, and finetuning) in ViT for multimodal FAS with RGB, Infrared (IR), and Depth.
Flexible-modal Deception Detection with Audio-Visual Adapter
no code implementations • 11 Feb 2023 • Zhaoxu Li, Zitong Yu, Nithish Muthuchamy Selvaraj, Xiaobao Guo, Bingquan Shen, Adams Wai-Kin Kong, Alex Kot
Detecting deception by human behaviors is vital in many fields such as custom security and multimedia anti-fraud.
Traceable and Authenticable Image Tagging for Fake News Detection
no code implementations • 20 Nov 2022 • Ruohan Meng, Zhili Zhou, Qi Cui, Kwok-Yan Lam, Alex Kot
Extensive experiments, on diverse datasets and unseen manipulations, demonstrate that the proposed tagging approach achieves excellent performance in the aspects of both authenticity verification and source tracing for reliable fake news detection and outperforms the prior works.
Toward domain generalized pruning by scoring out-of-distribution importance
no code implementations • 25 Oct 2022 • Rizhao Cai, Haoliang Li, Alex Kot
Filter pruning has been widely used for compressing convolutional neural networks to reduce computation costs during the deployment stage.
Enhancing Low-Light Images in Real World via Cross-Image Disentanglement
no code implementations • 10 Jan 2022 • Lanqing Guo, Renjie Wan, Wenhan Yang, Alex Kot, Bihan Wen
Images captured in the low-light condition suffer from low visibility and various imaging artifacts, e. g., real noise.
Towards Efficiently Evaluating the Robustness of Deep Neural Networks in IoT Systems: A GAN-based Method
no code implementations • 19 Nov 2021 • Tao Bai, Jun Zhao, Jinlin Zhu, Shoudong Han, Jiefeng Chen, Bo Li, Alex Kot
Through extensive experiments, AI-GAN achieves high attack success rates, outperforming existing methods, and reduces generation time significantly.
On Generating Identifiable Virtual Faces
no code implementations • 15 Oct 2021 • Zhuowen Yuan, Zhengxin You, Sheng Li, Xinpeng Zhang, Zhenxin Qian, Alex Kot
Our virtual face images are visually different from the original ones for privacy protection.
Benchmarking the Robustness of Spatial-Temporal Models Against Corruptions
1 code implementation • 13 Oct 2021 • Chenyu Yi, Siyuan Yang, Haoliang Li, Yap-Peng Tan, Alex Kot
The state-of-the-art deep neural networks are vulnerable to common corruptions (e. g., input data degradations, distortions, and disturbances caused by weather changes, system error, and processing).
Feature Distillation With Guided Adversarial Contrastive Learning
no code implementations • 21 Sep 2020 • Tao Bai, Jinnan Chen, Jun Zhao, Bihan Wen, Xudong Jiang, Alex Kot
In this paper, we propose a novel approach called Guided Adversarial Contrastive Distillation (GACD), to effectively transfer adversarial robustness from teacher to student with features.
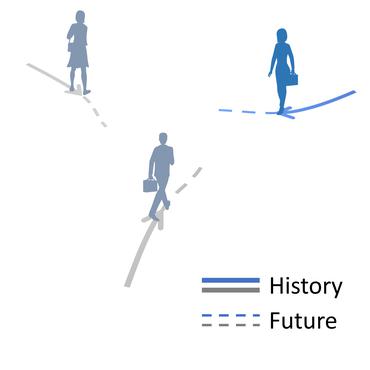
Multi-Camera Trajectory Forecasting: Pedestrian Trajectory Prediction in a Network of Cameras
1 code implementation • 1 May 2020 • Olly Styles, Tanaya Guha, Victor Sanchez, Alex Kot
To facilitate research in this new area, we release the Warwick-NTU Multi-camera Forecasting Database (WNMF), a unique dataset of multi-camera pedestrian trajectories from a network of 15 synchronized cameras.
AI-GAN: Attack-Inspired Generation of Adversarial Examples
1 code implementation • 6 Feb 2020 • Tao Bai, Jun Zhao, Jinlin Zhu, Shoudong Han, Jiefeng Chen, Bo Li, Alex Kot
Deep neural networks (DNNs) are vulnerable to adversarial examples, which are crafted by adding imperceptible perturbations to inputs.