Search Results for author: Yigit Alparslan
Found 11 papers, 4 papers with code
ATRAS: Adversarially Trained Robust Architecture Search
no code implementations • 13 Jun 2021 • Yigit Alparslan, Edward Kim
In this paper, we explore the effect of architecture completeness on adversarial robustness.
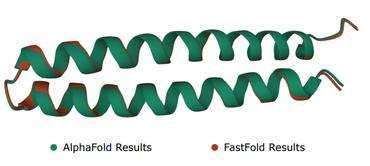
Functional Protein Structure Annotation Using a Deep Convolutional Generative Adversarial Network
no code implementations • 18 Apr 2021 • Ethan Moyer, Jeff Winchell, Isamu Isozaki, Yigit Alparslan, Mali Halac, Edward Kim
Identifying novel functional protein structures is at the heart of molecular engineering and molecular biology, requiring an often computationally exhaustive search.
Extreme Volatility Prediction in Stock Market: When GameStop meets Long Short-Term Memory Networks
1 code implementation • 1 Mar 2021 • Yigit Alparslan, Edward Kim
We compare both strategies to buying and holding one single share for the period that we picked as a benchmark.
Robust SleepNets
1 code implementation • 24 Feb 2021 • Yigit Alparslan, Edward Kim
In this study, we investigate eye closedness detection to prevent vehicle accidents related to driver disengagements and driver drowsiness.
Evaluating Online and Offline Accuracy Traversal Algorithms for k-Complete Neural Network Architectures
1 code implementation • 16 Jan 2021 • Yigit Alparslan, Ethan Jacob Moyer, Edward Kim
In this paper, we study compact neural network architectures for binary classification and investigate improvements in speed and accuracy when favoring overcomplete architecture candidates that have a very high-dimensional representation of the input.
Towards Searching Efficient and Accurate Neural Network Architectures in Binary Classification Problems
1 code implementation • 16 Jan 2021 • Yigit Alparslan, Ethan Jacob Moyer, Isamu Mclean Isozaki, Daniel Schwartz, Adam Dunlop, Shesh Dave, Edward Kim
Architecture size for a neural network contributes significantly to the success of any neural network.
Towards Evaluating Driver Fatigue with Robust Deep Learning Models
no code implementations • 16 Jul 2020 • Ken Alparslan, Yigit Alparslan, Matthew Burlick
We develop an eye model by using new Eye-blink dataset and a face model by using the Closed Eyes in the Wild (CEW).
Adversarial Attacks against Neural Networks in Audio Domain: Exploiting Principal Components
no code implementations • 14 Jul 2020 • Ken Alparslan, Yigit Alparslan, Matthew Burlick
We achieve 100% adversarial success rate (zero successful classification by DeepSpeech) on all 25 adversarial wave forms that we crafted.
Towards Evaluating Gaussian Blurring in Perceptual Hashing as a Facial Image Filter
no code implementations • 1 Feb 2020 • Yigit Alparslan, Ken Alparslan, Mannika Kshettry, Louis Kratz
In this paper, we would like to propose to experiment with effect of gaussian blurring in perceptual hashing for detecting misuse of personal images specifically for face images.
Adversarial Attacks on Convolutional Neural Networks in Facial Recognition Domain
no code implementations • 30 Jan 2020 • Yigit Alparslan, Ken Alparslan, Jeremy Keim-Shenk, Shweta Khade, Rachel Greenstadt
Next, we craft a variety of different black-box attack algorithms on a facial image dataset assuming minimal adversarial knowledge, to further assess the robustness of DNNs in facial recognition.
Perfecting the Crime Machine
no code implementations • 14 Jan 2020 • Yigit Alparslan, Ioanna Panagiotou, Willow Livengood, Robert Kane, Andrew Cohen
We use different techniques to extract various features including combining unsupervised learning techniques and try to predict the crime type.