Search Results for author: Nasir Memon
Found 21 papers, 9 papers with code
Mitigating the Impact of Attribute Editing on Face Recognition
no code implementations • 12 Mar 2024 • Sudipta Banerjee, Sai Pranaswi Mullangi, Shruti Wagle, Chinmay Hegde, Nasir Memon
To mitigate this issue, we propose two novel techniques for local and global attribute editing.
Alpha-wolves and Alpha-mammals: Exploring Dictionary Attacks on Iris Recognition Systems
no code implementations • 20 Nov 2023 • Sudipta Banerjee, Anubhav Jain, Zehua Jiang, Nasir Memon, Julian Togelius, Arun Ross
A dictionary attack in a biometric system entails the use of a small number of strategically generated images or templates to successfully match with a large number of identities, thereby compromising security.
Information Forensics and Security: A quarter-century-long journey
no code implementations • 21 Sep 2023 • Mauro Barni, Patrizio Campisi, Edward J. Delp, Gwenael Doërr, Jessica Fridrich, Nasir Memon, Fernando Pérez-González, Anderson Rocha, Luisa Verdoliva, Min Wu
Information Forensics and Security (IFS) is an active R&D area whose goal is to ensure that people use devices, data, and intellectual properties for authorized purposes and to facilitate the gathering of solid evidence to hold perpetrators accountable.
Fair GANs through model rebalancing for extremely imbalanced class distributions
no code implementations • 16 Aug 2023 • Anubhav Jain, Nasir Memon, Julian Togelius
We do so by generating balanced data from an existing imbalanced deep generative model using an evolutionary algorithm and then using this data to train a balanced generative model.
Identity-Preserving Aging of Face Images via Latent Diffusion Models
1 code implementation • 17 Jul 2023 • Sudipta Banerjee, Govind Mittal, Ameya Joshi, Chinmay Hegde, Nasir Memon
The performance of automated face recognition systems is inevitably impacted by the facial aging process.
Zero-shot racially balanced dataset generation using an existing biased StyleGAN2
1 code implementation • 12 May 2023 • Anubhav Jain, Nasir Memon, Julian Togelius
Facial recognition systems have made significant strides thanks to data-heavy deep learning models, but these models rely on large privacy-sensitive datasets.
A Dataless FaceSwap Detection Approach Using Synthetic Images
1 code implementation • 5 Dec 2022 • Anubhav Jain, Nasir Memon, Julian Togelius
Face swapping technology used to create "Deepfakes" has advanced significantly over the past few years and now enables us to create realistic facial manipulations.
GOTCHA: Real-Time Video Deepfake Detection via Challenge-Response
1 code implementation • 12 Oct 2022 • Govind Mittal, Chinmay Hegde, Nasir Memon
With the rise of AI-enabled Real-Time Deepfakes (RTDFs), the integrity of online video interactions has become a growing concern.
Diversity and Novelty MasterPrints: Generating Multiple DeepMasterPrints for Increased User Coverage
no code implementations • 11 Sep 2022 • M Charity, Nasir Memon, Zehua Jiang, Abhi Sen, Julian Togelius
This work expands on previous advancements in genetic fingerprint spoofing via the DeepMasterPrints and introduces Diversity and Novelty MasterPrints.
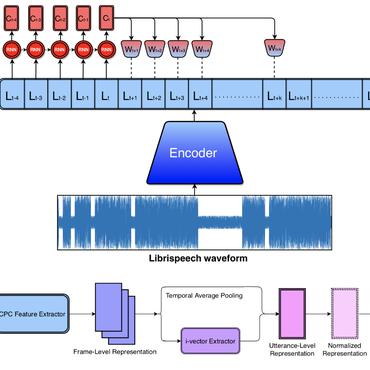
Dictionary Attacks on Speaker Verification
no code implementations • 24 Apr 2022 • Mirko Marras, Pawel Korus, Anubhav Jain, Nasir Memon
In this paper, we propose dictionary attacks against speaker verification - a novel attack vector that aims to match a large fraction of speaker population by chance.
Hard-Attention for Scalable Image Classification
1 code implementation • NeurIPS 2021 • Athanasios Papadopoulos, Paweł Korus, Nasir Memon
Can we leverage high-resolution information without the unsustainable quadratic complexity to input scale?
The Role of the Crowd in Countering Misinformation: A Case Study of the COVID-19 Infodemic
no code implementations • 11 Nov 2020 • Nicholas Micallef, Bing He, Srijan Kumar, Mustaque Ahamad, Nasir Memon
Concerned citizens (i. e., the crowd), who are users of the platforms where misinformation appears, can play a crucial role in disseminating fact-checking information and in countering the spread of misinformation.
Quantifying the Cost of Reliable Photo Authentication via High-Performance Learned Lossy Representations
1 code implementation • ICLR 2020 • Pawel Korus, Nasir Memon
Detection of photo manipulation relies on subtle statistical traces, notoriously removed by aggressive lossy compression employed online.
Empirical Evaluation of PRNU Fingerprint Variation for Mismatched Imaging Pipelines
no code implementations • 4 Apr 2020 • Sharad Joshi, Pawel Korus, Nitin Khanna, Nasir Memon
We assess the variability of PRNU-based camera fingerprints with mismatched imaging pipelines (e. g., different camera ISP or digital darkroom software).
Fusion of Camera Model and Source Device Specific Forensic Methods for Improved Tamper Detection
no code implementations • 24 Feb 2020 • Ahmet Gökhan Poyraz, Ahmet Emir Dirik, Ahmet Karaküçük, Nasir Memon
PRNU based camera recognition method is widely studied in the image forensic literature.
FiFTy: Large-scale File Fragment Type Identification using Neural Networks
1 code implementation • 16 Aug 2019 • Govind Mittal, Pawel Korus, Nasir Memon
We present FiFTy, a modern file type identification tool for memory forensics and data carving.
Cryptography and Security Multimedia
Neural Imaging Pipelines - the Scourge or Hope of Forensics?
1 code implementation • 27 Feb 2019 • Pawel Korus, Nasir Memon
This paper explores end-to-end optimization of the entire image acquisition and distribution workflow to facilitate reliable forensic analysis at the end of the distribution channel, where state-of-the-art forensic techniques fail.
Content Authentication for Neural Imaging Pipelines: End-to-end Optimization of Photo Provenance in Complex Distribution Channels
1 code implementation • CVPR 2019 • Pawel Korus, Nasir Memon
Forensic analysis of digital photo provenance relies on intrinsic traces left in the photograph at the time of its acquisition.
Kid on The Phone! Toward Automatic Detection of Children on Mobile Devices
no code implementations • 5 Aug 2018 • Toan Nguyen, Aditi Roy, Nasir Memon
In this work, we present multiple techniques to automatically detect the presence of a child on a smart device, which could be used as the first step on such systems.
Tap-based User Authentication for Smartwatches
no code implementations • 2 Jul 2018 • Toan Nguyen, Nasir Memon
This paper presents TapMeIn, an eyes-free, two-factor authentication method for smartwatches.
DeepMasterPrints: Generating MasterPrints for Dictionary Attacks via Latent Variable Evolution
no code implementations • 21 May 2017 • Philip Bontrager, Aditi Roy, Julian Togelius, Nasir Memon, Arun Ross
The proposed method, referred to as Latent Variable Evolution, is based on training a Generative Adversarial Network on a set of real fingerprint images.