Search Results for author: Pawel Korus
Found 7 papers, 5 papers with code
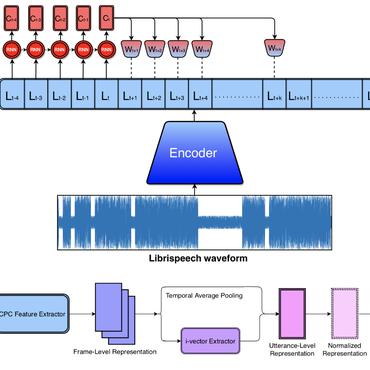
Dictionary Attacks on Speaker Verification
no code implementations • 24 Apr 2022 • Mirko Marras, Pawel Korus, Anubhav Jain, Nasir Memon
In this paper, we propose dictionary attacks against speaker verification - a novel attack vector that aims to match a large fraction of speaker population by chance.
Quantifying the Cost of Reliable Photo Authentication via High-Performance Learned Lossy Representations
1 code implementation • ICLR 2020 • Pawel Korus, Nasir Memon
Detection of photo manipulation relies on subtle statistical traces, notoriously removed by aggressive lossy compression employed online.
Empirical Evaluation of PRNU Fingerprint Variation for Mismatched Imaging Pipelines
no code implementations • 4 Apr 2020 • Sharad Joshi, Pawel Korus, Nitin Khanna, Nasir Memon
We assess the variability of PRNU-based camera fingerprints with mismatched imaging pipelines (e. g., different camera ISP or digital darkroom software).
FiFTy: Large-scale File Fragment Type Identification using Neural Networks
1 code implementation • 16 Aug 2019 • Govind Mittal, Pawel Korus, Nasir Memon
We present FiFTy, a modern file type identification tool for memory forensics and data carving.
Cryptography and Security Multimedia
Neural Imaging Pipelines - the Scourge or Hope of Forensics?
1 code implementation • 27 Feb 2019 • Pawel Korus, Nasir Memon
This paper explores end-to-end optimization of the entire image acquisition and distribution workflow to facilitate reliable forensic analysis at the end of the distribution channel, where state-of-the-art forensic techniques fail.
Content Authentication for Neural Imaging Pipelines: End-to-end Optimization of Photo Provenance in Complex Distribution Channels
1 code implementation • CVPR 2019 • Pawel Korus, Nasir Memon
Forensic analysis of digital photo provenance relies on intrinsic traces left in the photograph at the time of its acquisition.
Large-Scale and Fine-Grained Evaluation of Popular JPEG Forgery Localization Schemes
1 code implementation • 30 Nov 2018 • Pawel Korus
Over the years, researchers have proposed various approaches to JPEG forgery detection and localization.
Multimedia